Security & Risk Management

Welcome to my blog! My name is Mohamed Abdalla Ibrahim and I am a Cyber Security Specialist and IS security enthusiast. With over 15 years of experience in an enterprise environment, I have a strong understanding of the business risks related to IT. I am always seeking out the newest technologies to upgrade my knowledge and enhance my skills and qualifications in my field. I am self-motivated and have strong communication skills, and my greatest goal is to be a distinguished source of innovation in the IT field. Thank you for visiting my blog, and I hope you find the information and resources on this site helpful and informative
WannaCry Ransomware?
WannaCry ransomware is a crypto-ransomware worm that attacks Windows PCs. It’s a form of malware that can spread from PC to PC across networks (hence the "worm" component) and then once on a computer it can encrypt critical files (the "crypto" part). The perpetrators then demand ransom payments to unlock those files. The name was derived from strings of code detected in some of the first samples of the virus.
WannaCry has been called a "study in preventable catastrophes" because two months before it first spread around the world in 2017, Microsoft issued a patch that would have prevented the worm from infecting computers.[1] Unfortunately, hundreds of thousands of systems were not updated in time, and an unknown number of such systems remain vulnerable today.
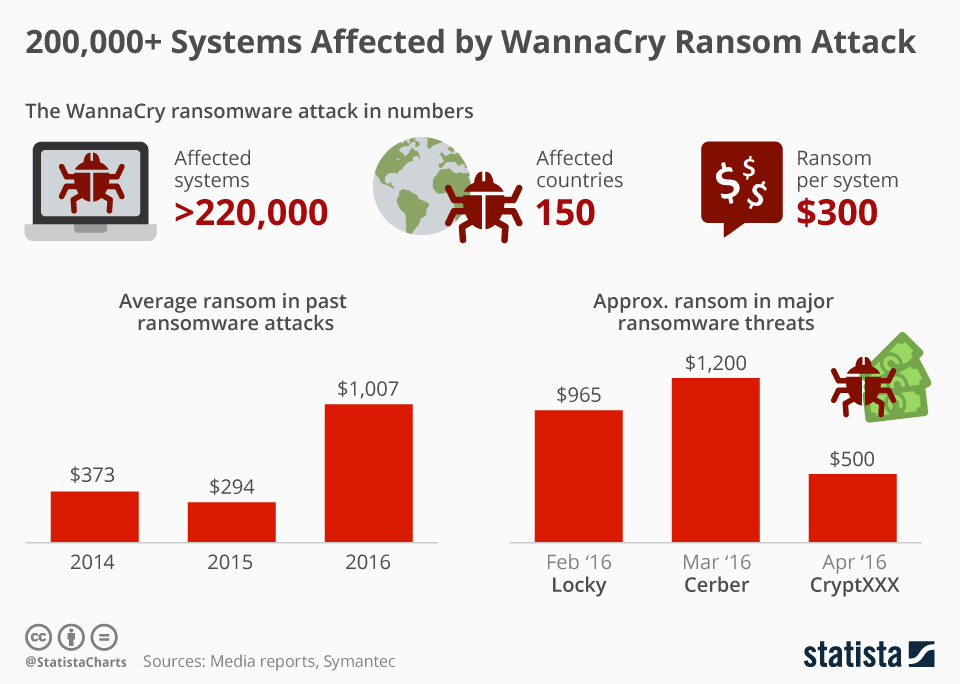
Ex : A massive ransomware attack has shut down work at 16 hospitals across the United Kingdom. According to The Guardian, the attack began at roughly 12:30 PM local time, freezing systems and encrypting files. When employees tried to access the computers, they were presented with a demand for $300 in bitcoin, a classic ransomware tactic. The result has been a wave of canceled appointments and general disarray, as many hospitals are left unable to access basic medical records. At least one hospital has canceled all non- urgent operations as a result.
Your Company {X Hospital } for Example just infected with wannacry
What Questions you should ask yourself:
- How do you are Governance your company?
- What Regulations you should comply with? And are you comply with it?
- Do you have InfoSec Security Program?
- Do you have InfoSec Security Policy, Standards, Procedures, Guidelines, or IRP?
- When was the last time you checked your BIA and reviewed your Risk Analysis & Assessment?
- When the last time you reviewed your policy, Patch Management, Configuration
- Management, BCP, DRP, Security Awareness plans…etc.?
- Which Framework did you are following when you created all the above policies and plans?
- Do you have the latest Security Controls, How you are using them?
- What are the KPI, KGI, and KRI you are using?

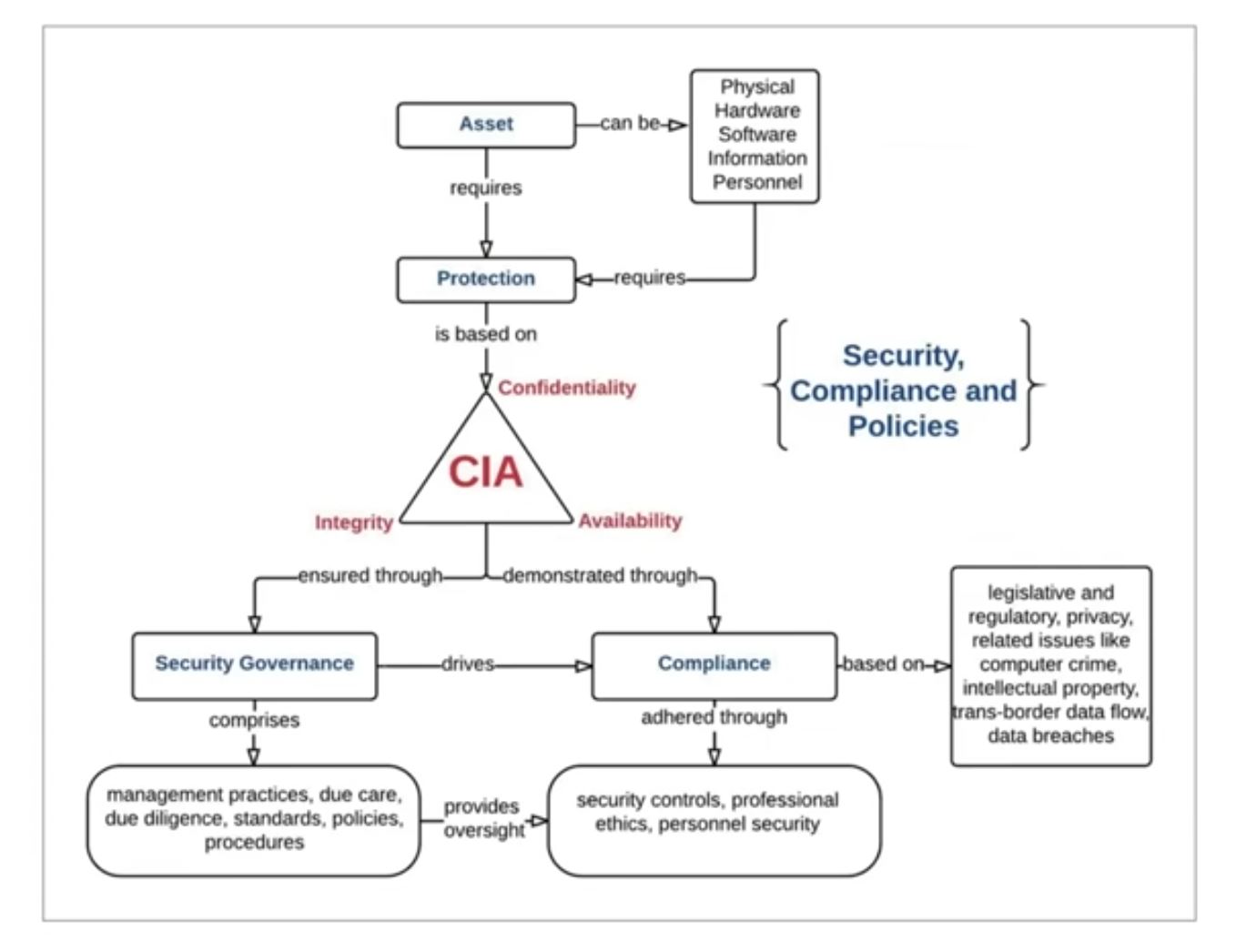
Protecting CIA
Information security :
is the practice of protecting Information and systems that contain information
Confidentiality:
Preserving authorized restrictions on information access and disclosure, including means for protecting personal privacy and proprietary information. Note – Encryption (At transit – TLS) (At rest - AES – 256)
Integrity:
Guarding against improper information modification or destruction and includes ensuring information non-repudiation and authenticity.
Availability:
Ensuring timely and reliable access to and use of information by authorized users.
Other concepts, conditions, and aspects of confidentiality include the following :
Sensitivity = the quality of information that could cause harm or damage if disclosed .mainting confidentiality of sensitive information helps to prevent harm or damage.
Criticality = the level to which information is mission-critical is its measure of criticality the higher the level of criticality, the more likely the need to maintain the confidentiality of the information. high level of. critically is essential to the operation or function of an organization
Other concepts, conditions, and aspects of integrity include the following :
Accuracy: being correct and precise.
Truthfulness: being a true reflection of reality.
Validity: Being factually or logically sound.
Non-repudiation: not being able to deny having performed an action or activity or being able to verify the origin of a communication event.
Other concepts, conditions, and aspects of Availability include the following :
Usability: The state of being easy to use learn or being able to understand and control the subject
Accessibility: the assurance that the widest range of subjects can interact with a resource regardless of their capabilities or limitations.
Timeliness: being prompt, on time, within a reasonable time frame, or providing a low latency response

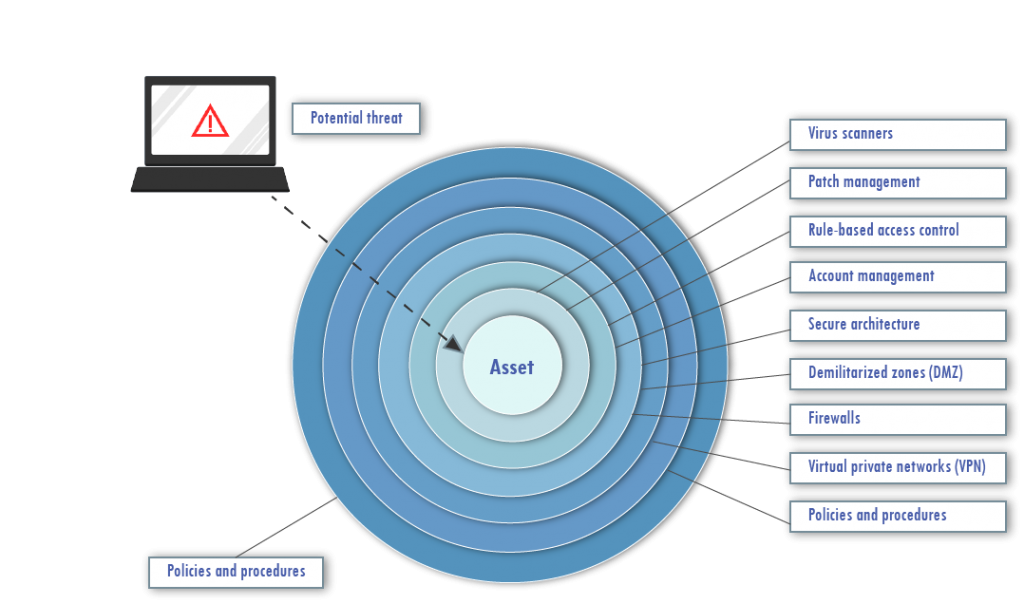
Protection mechanisms
Another aspect of understanding and applying concepts of confidentiality, integrity, and availability is the concept of protection mechanisms or protection controls.
Protection mechanisms are common characteristics of security controls.
Not all security controls must have them, but many controls offer their protection for confidentiality, integrity, and availability through the use of these mechanisms.
Some common examples of these mechanisms include:
- Using Multiple Layers or levels of access
- Employing Abstraction
- Hiding Data
- Using Encryption.
Layering : Layering, also known as defense-in-depth, is simply the use of multiple controls in a series.
-> No one in control can protect against all possible threats.
Using a multilayered solution allows for numerous, different controls to guard against whatever threats come to pass.
When security solutions are designed in layers, a failed control should not result in exposure of systems or data.
-> Using layers in a series rather than in parallel is important. Performing security restrictions in a series means linearly performing one after the other.
-> Using separate security systems creates a layered security solution.
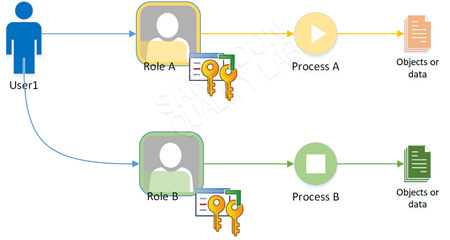
Abstraction
Abstraction is used for --->efficiency. -> Similar elements are put into groups, classes, or roles that are assigned security controls, restrictions, or permissions as a collective. Thus, the concept of abstraction is used when classifying objects or assigning roles to subjects.
The concept of abstraction also includes the definition of object and subject types or of objects themselves (that is, a data structure used to define a template for a class of entities).
Abstraction is used to define
- what types of data an object can contain,
- what types of functions can be performed on or by that object, and
- what capabilities does that object have.
Abstraction simplifies security by enabling you to assign security controls to a group of objects collected by type or function.
Data Hiding
Data hiding is exactly what it sounds like: preventing data from being discovered or accessed by a subject by positioning the data in a logical storage compartment that is not accessible or seen by the subject.
Forms of data hiding include keeping a database from being accessed by unauthorized visitors and restricting a subject at a lower classification level from accessing data at a higher classification level.
--> Preventing an application from accessing hardware directly is also a form of data hiding.
Data hiding is often a key element in security controls as well as in programming.
Encryption
Encryption is the art and science of hiding the meaning or intent of communication from unintended recipients. (More in Cryptography part)
Best Practices for CIA :
- Separation of duties (SOD)
- Mandatory Vacations
- Job Rotation
- Least privilege
- Need to know
- Dual Control
Separation of Duties (provide Integrity):
-> Two persons are involved to complete a critical task. For example, one person doing Backup, another person doing Restore.
This policy also helps prevent collusion as there are many individuals with discrete capabilities. Separation of Duties is a preventative control.
Dual control (aka Split Knowledge):
-> Two or more persons MUST to involved to complete a critical task. Example: To collect all money deposited in the ATM, we MUST have Two-person. Requiring more than one user to perform a task.
Mandatory Vacations:
Prevents an operator from having exclusive use of a system. Periodically that individual is forced to take a vacation and relegate control of the system to someone else. This policy is a detective control. We follow the same procedures we use in non-friendly Termination.
Job rotation: Similar in purpose to mandatory vacations, but with the added benefit of cross- training employees.
Access Aggregation leads to authorization Creep: As employees work at a company over time and move from one department to another, they often are assigned more and more access rights and permissions. This is commonly referred to as authorization creep.
Default no Access:
Least privilege (provide Confidentiality): Allowing users to have only the required access to do their jobs.
Aggregation In the context of least privilege, aggregation refers to the number of privileges that users collect over time.
Remember the following two things:
-Access aggregation lead to authorization creep. -We should determine the user's "Need to Know" level before we assign him the "Least privilege
Need to know (aka Need to Access) (provide integrity): In addition to clearance, users must also have a "need to know" to access classified data This principle ensures that subjects are granted access only to what they need to know for their work tasks and job functions. We decide for a user what he Needs to Know first then Least Privilege Compartmentalization Separate users into groups so info does not flow between groups Notice how this concept is opposite to the DevOps concept.
--> Organizations summarize their goals and objectives in mission and vision statements.
A Mission Statement defines the company's business, its objectives, and its approach to reaching those objectives.
A Vision Statement describes the desired future position of the company.
The goal Statement describes what we would like to do.
Objectives Statement describes desired capabilities or end states [ to accomplish the Goal] [ Your Desired State ].
Each organization should have :
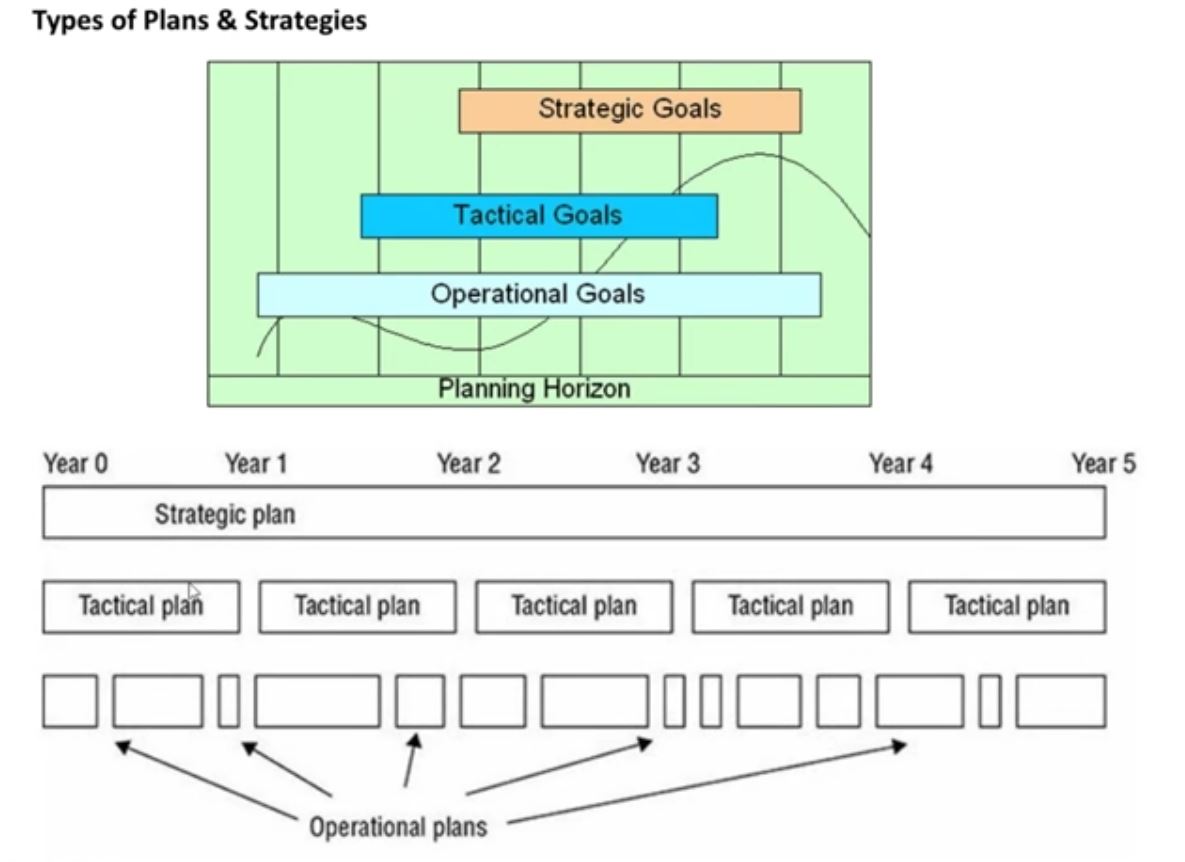
Plans Type
- Strategic Plan Duration up to 5 Years Ex: Risk Assessment
- Tactical Plan Duration Maximum of 1 year Ex: Project budget, staffing, etc
- Operational Plan Duration A few months EX: Patching computers, Updating AV signatures, Daily network administration.
So, We should know the :
1-InfoSec Strategy Objectives 2-Metrics that determine if those objectives are being achieved.
--- InfoSec Strategy has Road Map and [Resources and Constraints].
--- The strategy Action plan executes the strategy itself.
The action plan will include:
- Gap Analysis
- Policy Development
- Standards Development
- Training and Awareness
- Action Plan Metrics

Types of Plans & Strategies
The Security Management planning team devolves 3 types of plans:
*Strategic Plan
- A strategic plan is a long-term plan that is fairly stable.
- It defines the organization's security purpose.
- It also helps to understand security function and align it to the goals, mission, and objectives of the organization.
It's useful for about five years if it is maintained and updated annually.
The strategic plan also serves as the planning horizon.
A strategic plan should include a risk assessment.
*Tactical plan
The tactical plan is a midterm plan developed to provide more details on accomplishing, the goals outlined in the strategic plan or can be crafted ad-hoc based upon unpredicted events.
A tactical plan is typically useful for about a year and often prescribes and schedules the tasks necessary to accomplish organizational goals.
- Some examples of tactical plans are project plans, acquisition plans, hiring plans, budget, plans, maintenance plans, support plans, and system development plans.
*Operational Plan
An operational plan is a short-term, highly detailed plan based on strategic and tactical plans.
It is valid or useful only for a short time. Operational plans must be updated often (such as monthly or quarterly) to retain compliance with tactical plans.
Operational plans spell out how to accomplish the various goals of the organization.
They include resource allotments, budgetary requirements, staffing assignments, scheduling, and step-by-step or implementation procedures.
Operational plans include details on how the implementation processes comply with the organization's security policy. Examples of operational plans are training plans, system deployment plans, and product design plans.
Regulation
- The purpose of any regulation is to eliminate choice.
- Regulation is intended to prevent shortcuts while setting minimum requirements of control.
Example : SOX,GLBA,PCI-DSS,HIPAA
- All Regulations require government offices & business enterprises to process two components:
Evidence of Operational Integrity
Evidence of Internal Controls to protect valuable assets
Two types of statements are contained in all regulations:
Recommended (Discretionary) SHOULD (recommendation) Ex: suggested mgmt responsibilities
Required (Mandatory) SHALL "Shall" indicates the statement is a commandment of Compliance (it is not optional)
Compliance
- The action or fact of complying with a wish or command.
- Organizations must comply even if it means that compliance will cause the organization to lose money.
- you must write the penalties

Governance
- Is all about leading (to Rule) Organization.
- To governs is to lead by the position of authority, set the rules, designate priorities, excises good decisions, and actively monitor the risk.
Governance refers to "all the processes of governing, whether undertaken by a government, market or network, whether over a family, tribe, formal or informal organization, or territory and whether through the laws, norms, power or language."
Six Assets need to be Governed: Human, Financial, Physical, Relationships, Intellectual property and Information and IT Assets
Information security governance is: the sum of the processes, procedures, guidelines, and regulations that dictate the executive oversight of an organization's information security infrastructure.
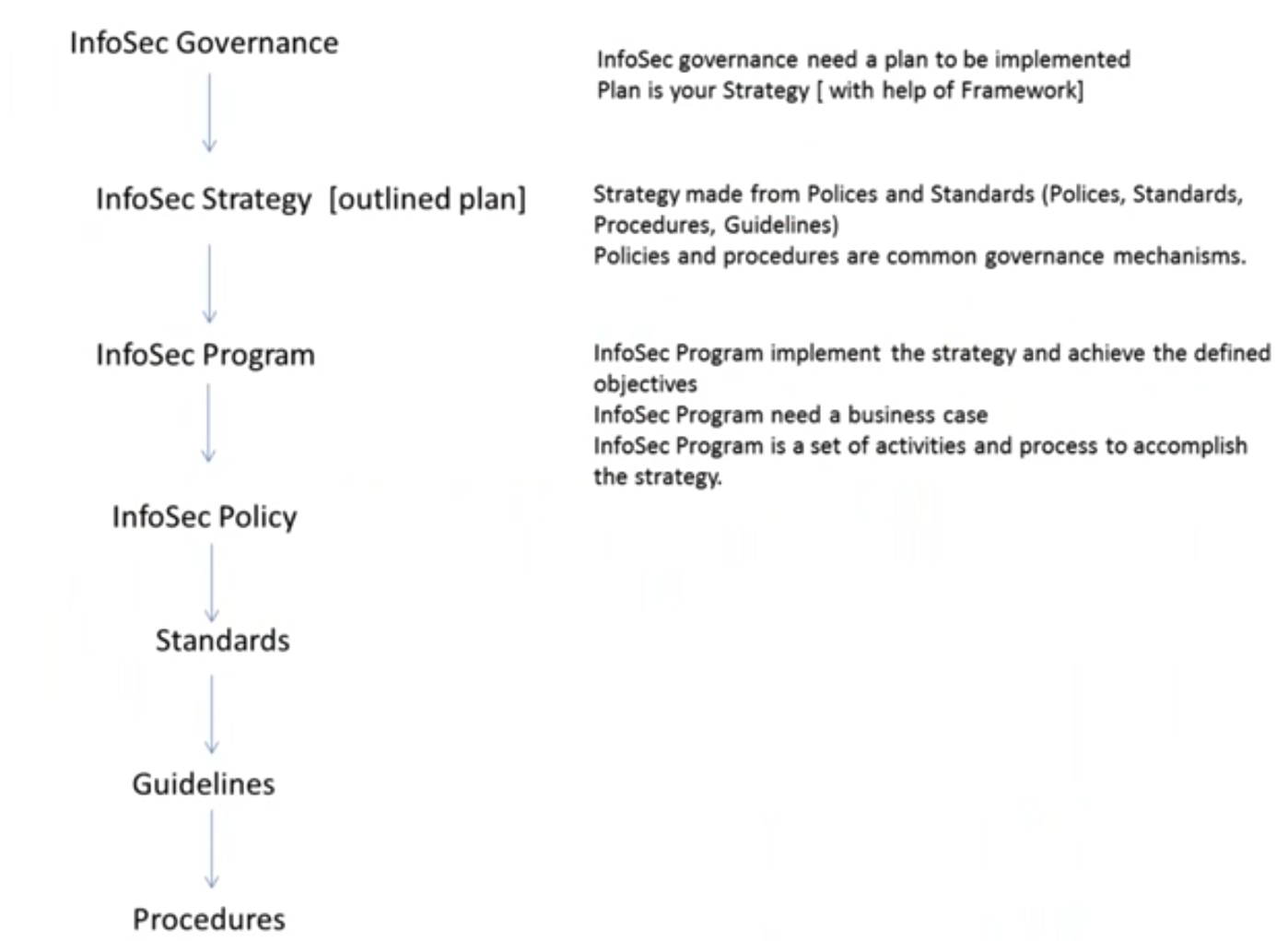
InfoSec Governance:
it is all about Security, control, and optimization of information.
Aim to Minimize InfoSec risk & Maximize infoSec value
It ongoing process control of info to meet legal, regulatory, risk, and business
demands.
Must be aligned with org goals
To create an infoSec governance program you need to understand the objectives of each business unit
InfoSec governance is primary is driven by business strategy
To create Effective InfoSec Governance it should follow Top-Down Approach
* Information security governance should be considered a part of IT governance and the board of directors should:
- Be informed about information security
- Set direction to drive policy and strategy
- Provide resources for security efforts
- Assign management responsibilities
- Set priorities
- Support changes required
- Define cultural values related to risk assessment
- Obtain assurance from internal or external auditors
- Insist that security investments are made measurable and reported on for the program effectiveness.
Management should:
- Write security policies with business input
- Ensure that roles and responsibilities are defined and clearly understood
- Identify threats and vulnerabilities
- Implement security infrastructures and control frameworks (standards, guidelines, baselines, and procedures)
- Ensure that policy is approved by the governing body
- Establish priorities and implement security projects on time
- Monitor breaches
- Conduct periodic reviews and tests
- Reinforce awareness education as critical
- Build security into the systems development life cycle
- That is why we say Management is different than governance
The outcomes of information security Governance
The objective of Information Security governance is to develop, implement and manage a Security Program. that achieve the following six basics outcomes:
- Strategic alignment: aligning information security with business strategy to support organizational objectives such as security solutions fit for enterprise process that takes into account the culture governance style, technology, and stricture of the organization.
- Risk Management: executing measures to mitigate risk and reduce potential impacts on information resources to an acceptable level.
- Value Delivery: optimizing security investments in support of business objectives
- Resource optimization: using infoSec knowledge and infra efficiently and effectively,
- Performance measurement: monitoring and reporting on the InfoSec process to ensure that objectives are achieved.
- Integration: integrating all relevant assurance factors to ensure that process operates as intended from end to end.

Here is an example:
The organization CareerSearchCo, which is in the online career search and recruiting the business has the following as its mission statement:
-Be the best marketplace for job seekers and recruiters
Here are its most recent strategic objectives:
-Integrate with leading business social network Linkedin Develop an API to facilitate long-term transformation into a leading career and recruiting platform
To meet these objectives, CareerSearchCo has developed a security strategy that includes the following:
-Ensure Internet-facing applications are secure through developer training and application vulnerability testing
Security and metrics would then include these: -Percentage of software developers not yet trained -Number of critical vulnerabilities identified -Time to remediate critical and high vulnerabilities Based on these criteria, these metrics are all measurable, they align with the security strategy and they are all leading indicators.
The higher these metrics, the more likely a breach would occur that would damage CareerSearchCo's reputation and ability to earn new business contracts from large corporations.
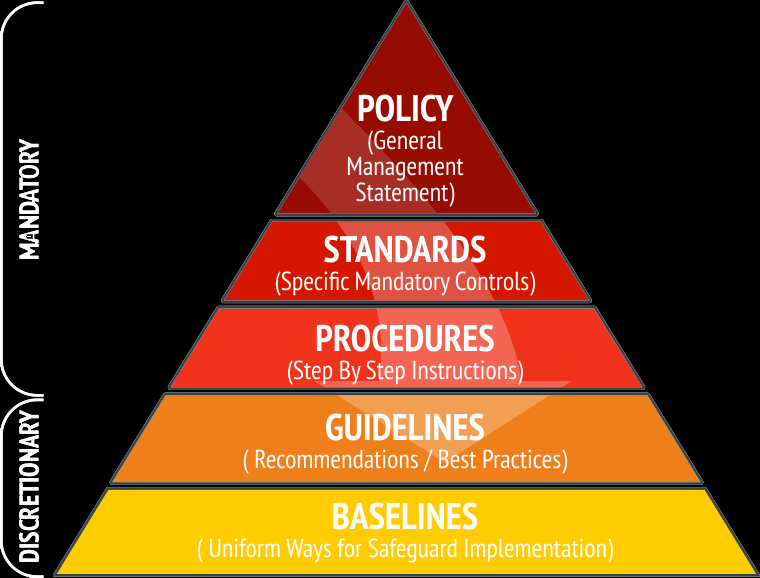
Policies
- It means Goals, 3 pages High-level document, it shows "what to protect"
- It provides general control covering activities within the organization by staff, vendors, clients……etc.
- It states the objectives "who will responsible for decisions, administration, and penalties for noncompliance.
- The overall general statement produced by senior management /what expectations of correct usage
- Approval for policy made by executive level)
- Compliance is Mandatory for Policy
Standards
WHAT Technologies & Methodologies
- Should add to Policy, the policy has no meaning without standards
- It is a definition of requirements, a mid-level document.
- It includes' "what teach to use & measurement points to obtain compliance"
- Describes the specific use of technology, often applied to hardware and software.
- Refer to mandatory activities or rules / Regulatory compliance /Mandated (should happen) based on compliance.
Standards Categories:
- Regulatory
- Industry
- Organizational
- Personal (your own high ethics = high standards)
Guidelines
HOW [Best Practice & Recommendations]
- Its general instructions, it's Discretionary, it Does that & Not that.
- Its advice for how organization objectives might be obtained.
- It has no meaning without adding to its Procedures.
- such as "To create a strong password…
Procedures
HOW [Step by Step]
- Its How-To instructions for success.
- Its detailed instructions )for accomplishing a task.
- Its details are written in Step-by-Step format.
- It includes "Best Practice" which suggested developing your procedures.
- They are low-level and specific.
- Compliance is Mandatory for procedures
Baselines
Template for comparison, measure deviation from normal / Standardized solution / Allows us to find and measure deviations.
A baseline is a minimum level of security that a system, network, or device must adhere to.
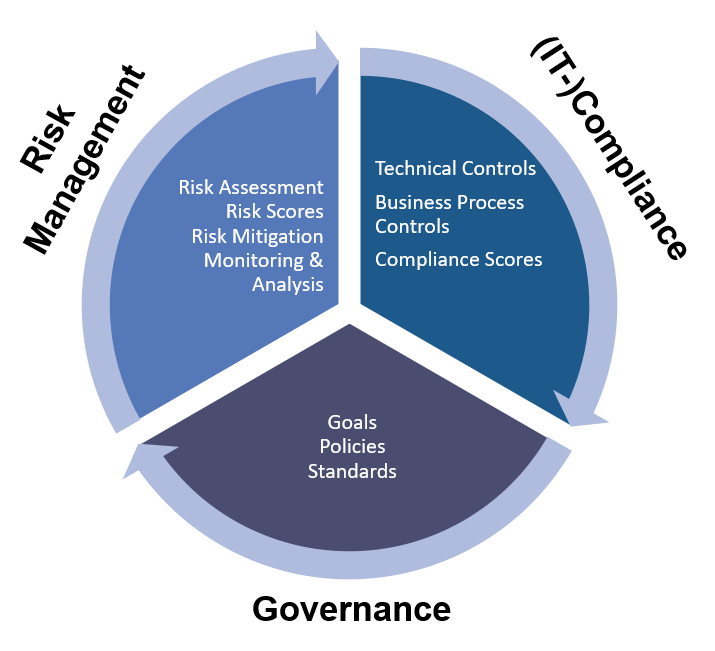
GRC
- GRC is a term that reflects an approach that org can adopt to integrate these three areas.
- These three areas overlap with many activities within org such as internal audits, compliance programs (SOX act, HIPAA), incident management, Enterprise Risk Management ERM…etc.
- GRC always focused more on IT, Finance, and legal than other areas
- GRC used to improve Risk Management & ensure Compliance
- GRC is a recent effort to address integration issues between the major functions of Governance, Risk management, and Compliance.
- GRC is an emerging approach primarily for achieving assurance process integration
Organization Security Program Policy
Components of Organization security program policy:
- Purpose
- Scope
- Responsibilities
- Compliance
To know more about policies kindly check this link https://www.sans.org/information-security-policy/

Chief security officer (CSO) or chief information security officer (CISO):
The CSO or CISO is tasked with ensuring data and systems security. In general, a CSO is responsible for physical as well as digital security,
while a CISO is only in charge of digital security.
In some organizations, the CISO reports to the chief operating officer (COO) or the CEO, but in some organizations, the CISO may report to the CIO, chief legal counsel, or another person in the organization.
Responsibilities of the Information Security Officer [CISO]:
- Communicate Risks to Executive Management
- Budget for Information Security Activities
- Ensure the Development of Policies, Procedures, Baselines, Standards, and Guidelines
- Develop and Provide Security Awareness Program
- Understand Business Objectives
- Maintain Awareness of Emerging Threats and Vulnerabilities
- Evaluate Security Incidents and Response
- Develop Security Compliance Program
- Establish Security Metrics
- Participate in Management Meetings
- Ensure Compliance with Government Regulations
- Assist Internal and External Auditors
- Stay Abreast of Emerging Technologies
Security Steering Committee
Many organizations from a security steering committee, consisting of stakeholders from many (if not all) of the organization's business units, departments, functions, and principal locations.
To ensure that all stakeholders are impacted by security considerations A steering committee may have a variety of responsibilities, including the following:
- Risk treatment deliberation and recommendation
- Discussion and coordination of IT and security projects
- Review of recent risk assessments
- Discussion of new laws, regulations, and requirements
- Review of recent security incidents
| Receive reports and establish metrics to monitor the value provided by major security initiatives and the current state of security.
| Send summarized reports to executive management.
Common Topics & Agendas & Decisions for a Security Steering Committee include:
- Security Strategy & Integration efforts especially integrating Security with Business units activities.
- Specific actions and progress relative to business unit support of the InfoSec Program Functions and vice versa.
- Emerging risk, business unit security practices, and compliance
Business Process and Business Asset Owners [Data Owner /Information Owner]
Business process and asset owners are typically non-technical personnel in management positions in an organization.
The responsibilities of business process and business asset owners include the following:
• Access grants Asset owners decide whether individuals or groups should be given access to the asset, as well as the level and type of access. Example access types include combinations of read-only, read-write, create, and delete.
• Access revocation Asset owners should also decide when individuals or groups no longer require access to an asset, signaling the need to revoke that access.
• Access reviews Asset owners should periodically review access lists to see whether each person and group should continue to have that access. Access reviews may also include access activity reviews to determine whether people who have not accessed assets still require access to them.
• Configuration Asset owners determine the configuration needed for assets and applications, ensuring their proper function and support of applications and business processes.
• Function definition In the case of business applications and services, asset owners determine which functions will be available, how they will work, and how they will support business processes. Typically, this definition is constrained by functional limitations within an application, service, or product.
• Process definition Process owners determine the sequence, steps, roles, and actions carried out in their business processes.
• Physical location Asset owners determine the physical location of their assets.
Custodial Responsibilities [Custodian / Steward] People in IT Dept act as a proxy for asset owners and make access grants and other decisions on their behalf.
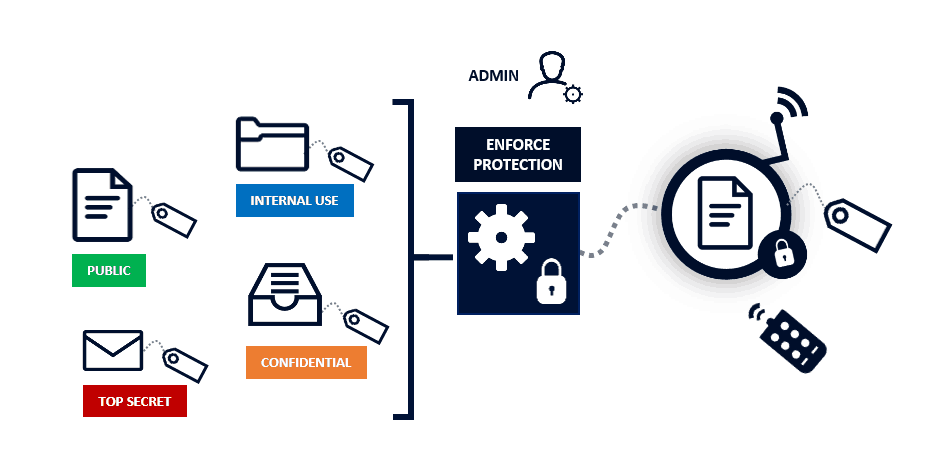
The data owner (also called information owner or business owner) is a management employee (executive or senior ) responsible for ensuring that specific data is protected. determine data sensitivity labels and the frequency of data backup. A company with multiple lines of business may have multiple data owners. The data owner performs management duties; custodians perform the hands-on protection of data. information owner has the final responsibility for authorizing InfoSec system access
| Classifying info is the Responsibility of the data owner
Custodians These individuals take care of information on behalf of the data owner, taking care to be sure data is properly backed up and protected from losses, and accessed only by authorized entities .provide hands-on protection of assets such as data. They perform data backups and restoration, patch systems, configure antivirus software This role is usually filled by the IT or security department
The End-user must follow the rules; they must comply with mandatory policies, procedures, standards, etc. responsible for protecting information assets daily through adherence to the security policies that have been communicated.
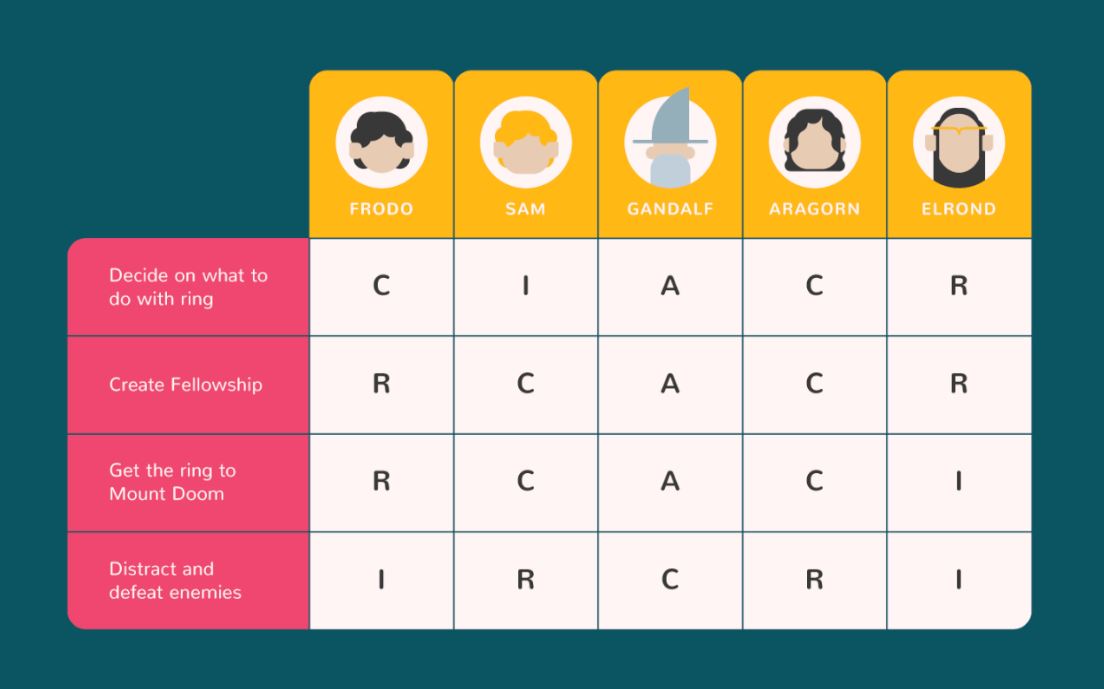
What is the RACI model?
| A Model used to help define roles and responsibilities. RACI stands for Responsible, Accountable, Consulted, and Informed
- Those in the R = RESPONSIBLE role for a given activity are charged with actually executing or performing the activity or task.
- The single entity in the A = ACCOUNTABLE role owns the task or activity and must answer for its outcomes. Only one party can be accountable for a given task/activity.
- Those in the C= CONSULTED role to review and provide advice and authorization around the task or activity.
- Those in the I= INFORMED role receive updates as the task or activity progresses.
Note: Not all the rows have one and only one accountable and at least one responsible.
Liabilities (Responsibilities)
Who is responsible for the security within an organization?
Senior management
Example:
Developing and implementing a security policy is evidence of due care and due diligence on the part of senior management. Due care is using reasonable care to protect the interests of an organization. [Ensuring that "best practices" are implemented and followed]
Due diligence is practicing the activities that maintain the due care effort. [Continuously monitoring]
Due diligence is the management of due care.
Senior management must show due care and due diligence to reduce their culpability and liability when a loss occurs.
Prudent man rule: Acting responsibly and cautiously as a prudent man would

Types of attacks :
- Wireless Attacks
- Network Attacks
- Web Application Attacks
- Malware Attacks
- Mobile Attacks
- Virtualization Attacks
- Cloud Attack
- loT Attacks
But who is the Attack Actor [aka Threat Agent, Threat Actor]?
Types of actors :
| threat actors can range from beginners probing to the highly organized state
- Script Kiddies
- Active
- Organized crime
- Nation-state /APT
- Insiders
- Competitors
Advanced Persistent Threat (APT).
This is a military term that has been around for ages it is commonly a group of attackers, not just one hacker, who combines knowledge and abilities to carry out whatever exploit that will get them into the environment they are seeking.
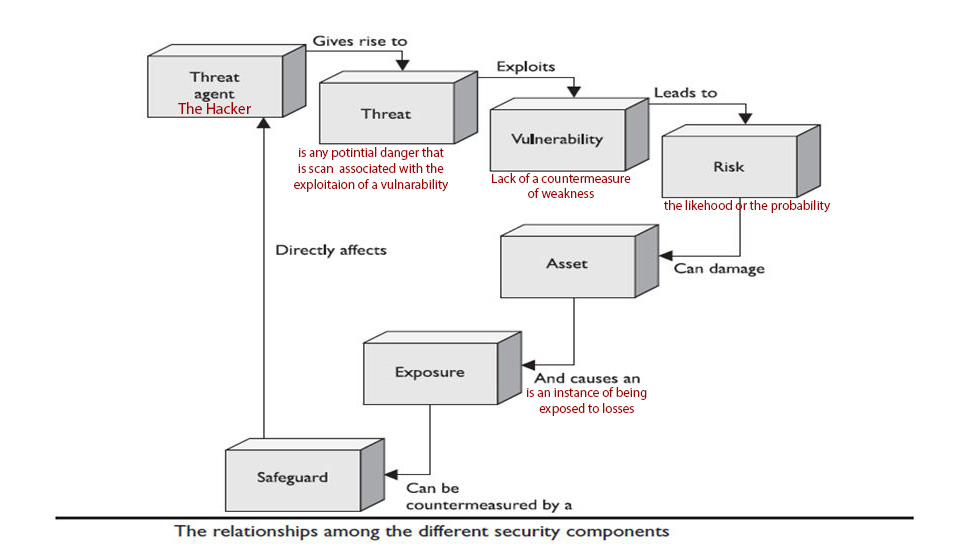
Countermeasure is an action, device, procedure, or technique that reduces a threat, a vulnerability, or an attack by eliminating or preventing it, by minimizing the harm it can cause, or by discovering and reporting it so that corrective action can be taken.
Countermeasure = Reactive
A safeguard is a measure taken to protect someone or something or to prevent something undesirable.
Safeguard = Proactive
Security controls are safeguards or countermeasures to avoid, detect, counteract, or minimize security risks to physical property, information, computer systems, or other assets.
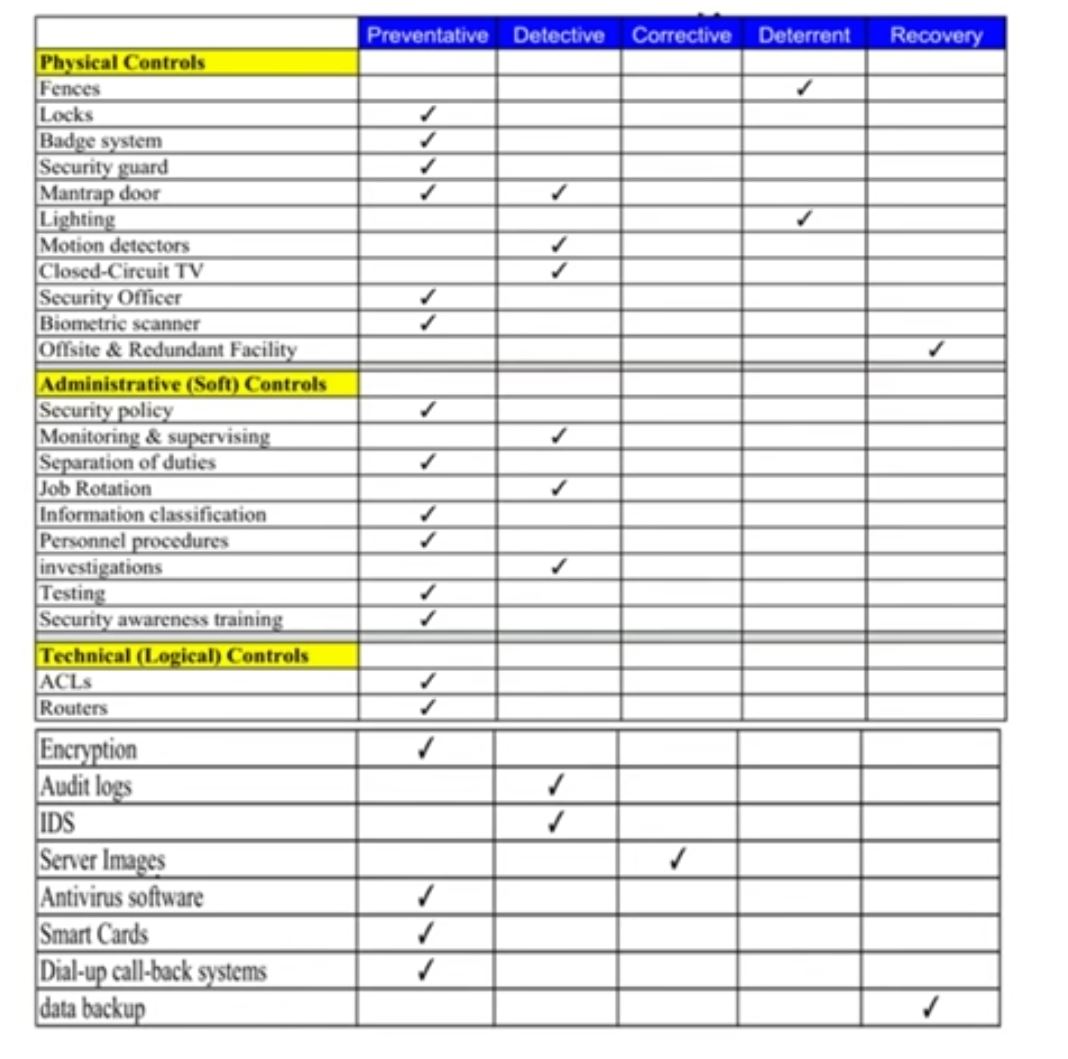
Security / Access Control Categories and Types
There are three categories of access control:
- Technical
- Administrative
- Physical
These controls should be countermeasures for vulnerabilities
Technical (Logical) controls: Is a control that is put into place to restrict access. work to protect access, system access, network arch, control zones, auditing, encryption, protocols Logical Example: Biometrics for Authentication Technical Example: Constrained user interface
Administrative (Soft) Control: Is a control that dictates how security policies are implemented to fulfill the company's security goals? it includes: policies, procedures, personal control, supervisory structure, security training, and testing Example: Labeling of sensitive data
Physical control: Is a control that is implemented to secure physical access to an object such as a building room computer includes: badges, locks, guards, network segregation, perimeter security, computer controls, work area separation, backups, cabling Example RFID Badge
These access controls categorized can fall into one of 7 Different Types:
Preventative controls prevent security breaches and avoid risks
Detective controls detect security breaches as they occur
Corrective controls restore control and attempt to correct any damage that was inflicted during the security breach
Determent controls deter potential violations - make the hacker think twice before he started his attack Ex: fake sign watch out dogs and you don't have dogs.
Recovery controls restore resources
Compensative controls provide an alternative control if another control maybe expensive, all controls are generally considered Compensative. FW we add IPS to prevent residual Risk.
Directive controls provide mandatory controls based on regulations
EX :
Up to this point we know
- What we need to accomplish (availability, integrity, confidentiality)
- What the tools we can use (administrative, technical, physical controls)
- How to talk about this issue (vulnerability, threat, risk, control).
Now time to develop an organization's Security Program,
let's first explore what not to do, which is referred to as security through obscurity.
Security through obscurity is assuming that your enemies are not as smart as you are and that they cannot figure out something that you feel is very tricky.
Ex : A common example of practicing security through obscurity is to develop cryptographic algorithms in-house instead of using algorithms that are commonly used within the industry.
Security through obscurity is a BAD and not good choice So better to develop an organization-wide security program
We need a detailed plan to follow to properly build our security program. So, We need a Framework to follow.
But what is the difference between Framework & Methodology?
A framework is an international standard of best practices and it is to be used as a toolbox, from which you choose processes, tools, and techniques to help you deliver projects successfully.
Example:
Control Objectives for Information and Related Technology (COBIT) US National Institute of Standards and Technology (NIST) PMI PM project management body of knowledge
A framework is a logical structure.
- The intent of a framework is to document and organize processes.
A framework can also be the basis of a common evaluation by:
- Internal stakeholders
- External auditors
- Third parties
A methodology has already taken the processes, tools, and techniques and developed them into a standardized approach to managing projects in a certain way. A system of methods used in a particular area of study or activity.
Example:
- Lean practices
- Kanban
- Six Sigma
---> How to Apply Framework ? = Methodology
Written by : Mohamed Abdalla Ibrahim
PMP | CISM | ITIL | CEH | Azure Architect | Azure Security Engineer | IBM Cybersecurity Analyst