CYBER SECURITY (Penetration Testing Prerequisites) 1.5 Internet Protocols (IP)

Welcome to my blog! My name is Mohamed Abdalla Ibrahim and I am a Cyber Security Specialist and IS security enthusiast. With over 15 years of experience in an enterprise environment, I have a strong understanding of the business risks related to IT. I am always seeking out the newest technologies to upgrade my knowledge and enhance my skills and qualifications in my field. I am self-motivated and have strong communication skills, and my greatest goal is to be a distinguished source of innovation in the IT field. Thank you for visiting my blog, and I hope you find the information and resources on this site helpful and informative
How does Studying IP Support your pentesting career? Allows you to understand network attacks, use networking attacking tools at their maximum, understand attacking scripts and modify them, and study other network protocols. The internet protocol (IP) is the protocol that runs on the internet layer of the internet protocol suite, also known as TCP/IP. IP is in charge of delivering the datagrams. Any host on a computer network, be it a private network or the internet, is identified by a unique IP address.
Ex: The vast majority of networks run IP version 4 (IPv4) An IPv4 address consists of four bytes or octets of 8 bits. 192.168.1.1
IP/Mask
To find the network part you have to perform a bitwise AND operation between the netmask and the IP address.
In the following example we are going to see how to find the network part of the IP address/mask pair :
192.168.33.12/255.255.224.0
Convert the octets in binary form :
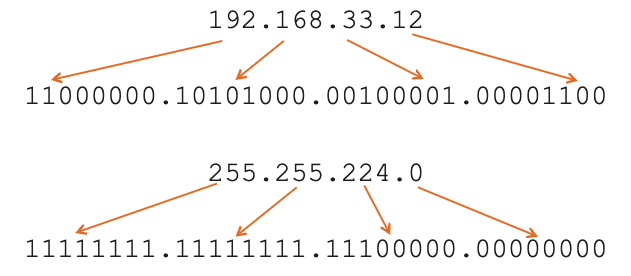
Perform the bitwise AND :
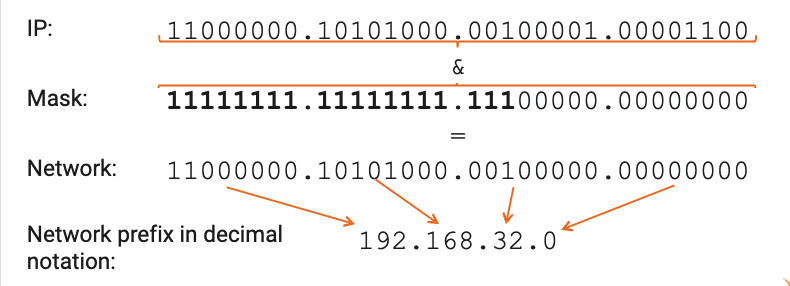
192.168.32.0 is the network prefix . you can identify the network by using the following notation: 192.168..32.0/255.255.224.0
Or as the netmask is made by 19 consecutive "1" bits: 192.168.32.0/19
The latter is the class Inter-Domain Routing (CIDR) notation
Network and Broadcast Address : There are two special addresses:
- One with the host part made by all Zeros
- Another with the host part made by all ones.
You can do your own research to know more about IP addresses and Mask Hosts, it's really a VIP topic not only for pen-test but also in. the cyber security field.
In the next article, I will write about Routing.
Written by : Mohamed Abdalla Ibrahim
PMP | CISM | ITIL | CEH | Azure Architect | Azure Security Engineer | IBM Cybersecurity Analyst