Asset Security

Welcome to my blog! My name is Mohamed Abdalla Ibrahim and I am a Cyber Security Specialist and IS security enthusiast. With over 15 years of experience in an enterprise environment, I have a strong understanding of the business risks related to IT. I am always seeking out the newest technologies to upgrade my knowledge and enhance my skills and qualifications in my field. I am self-motivated and have strong communication skills, and my greatest goal is to be a distinguished source of innovation in the IT field. Thank you for visiting my blog, and I hope you find the information and resources on this site helpful and informative

What is the asset :
•Anything you want to protect and it can be :
Tangible: Ex: computer Assets, servers, people.
Or
Intangible: Ex: Corporate image.
The asset can be compromised stolen or modified and the data secret can be disclosed asset can be hardware or software, process, product, or infrastructure that is valuable to the organization.
-The level of protection is based on the value of an asset to the business.
How to Protect

Group asset based on its type to facilitate protecting it such as : •Tangible or intangible •Pysical or virtual •Computing or non-computing •Information assets •Personal assets (Employee, Contractors, Third party) •Cloud assets
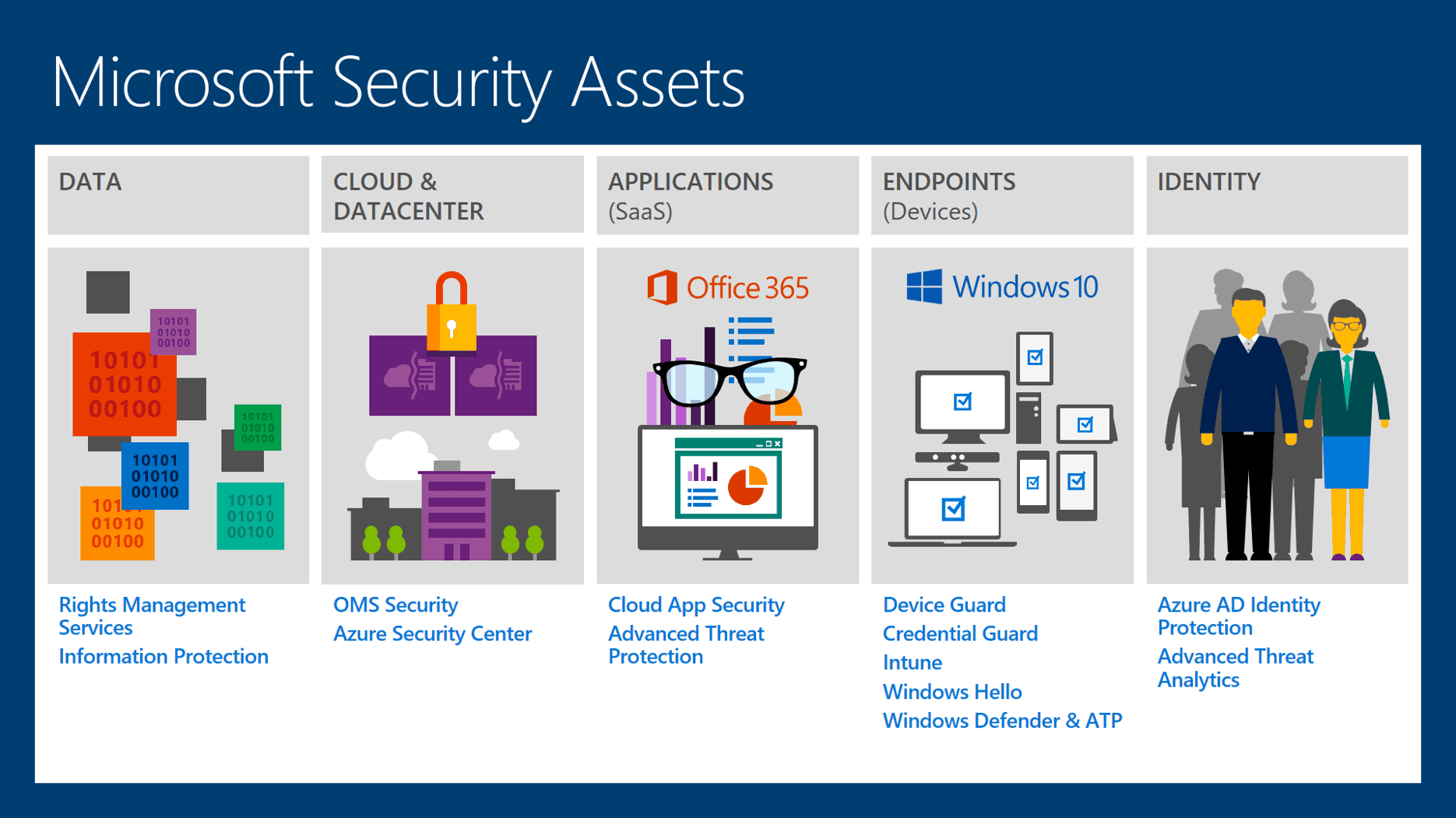
DATA : PII (Personally identifiable information) IP (Intellectual property) NPI (Non-public information) PHI (Protected Health information)
Protecting assets : Data at reset Data in motion in (transit) Data in use
Information Classification

There are two kinds of data classification : For Commercial business : -Confidential -Private -Sensitive -Public
For Military purposes or GOV
-Top secret -Secret -Confidential -Sensitive but unclassified -Unclassified

Classification Program:
You have to do the following tasks in the same sequence :
- Create an information asset inventory.
- Classification of information.
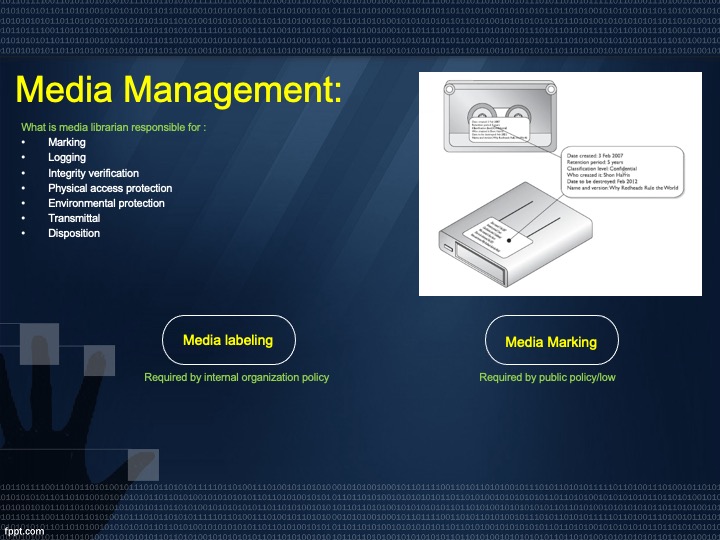
- Information labeling.
- Handling of assets.
Data Classification procedures :
- Define classification levels
- Specify the criteria that will determine how data is classified
- Identify the data owners who will responsible for classifying the data
- Identify the data custodian who will responsible for maintaining data and its security level
- Indicate the security controls or protection machinists required for each classification level
- Document any expectations to the previous classification issues
- Indicate the methods that can be used to transfer custody of information to the different data owner
- Create procedures to periodically review the classification and ownership
- Indicate procedures for declassifying the data
- Integrate these issues into the security awareness
Also, there are criteria parameters you can use to determine the sensitivity : The usefulness of data The value of data The age of data The level of damage that could be caused if the data were disclosed The level of damage that could be caused if the data is modified or corrupted Legal, regulatory, or contractual responsibility to protect the data Effects the data has no security Who should be able to access the data Who should maintain the data Who should be able to reproduce the data The lost opportunity that could be incurred if the data were not available or were corrupted
We also can't avoid the role of the Asset Owner (system owner): The Asset owner play important roles such as
-Develops a system security plan -Maintain the system security plan -Ensure that the system users and support personnel receive appropriate security training -Update system security plan -Assist in implementation, identification, and assessment of the common security control
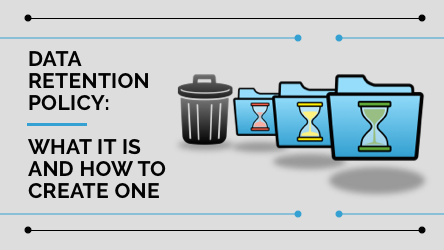
Important rules we should consider : Retention policy What data do we keep? How long do we keep this data? Where do we keep this data? Ex: business documents, invoices, human resources files, tax records Legal correspondence.
Privacy policy
-What personal data is collected? -Why do we collect this data and how do we use it? -To whom do we share this data? -Who owns the collected? -What rights does the subject of this data have with regard to? -When do we destroy the data? -What specific laws or regulations exist that pertain to this data
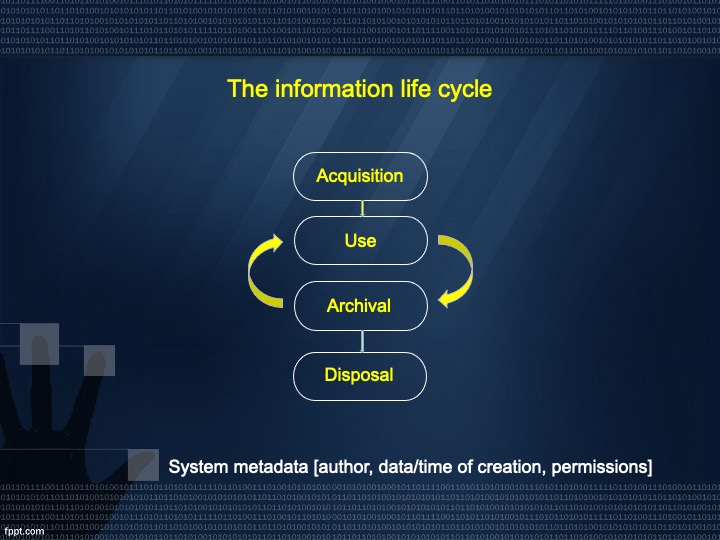
The information life cycle
Supply Chain Management (SCM)
Is a system of organization, people, activities, information, and resources involved in moving a product or a service from supplier to the customer
Supply chain Risk : Physical damage to tangible assets, and can include digital assets too Ex: ccleaner malware
Disposal Methods
Purging: making data unrecoverable even with extraordinary effort such as digital forensics in the laboratory. -remove data so it can’t be reconstructed by any known technique
Sanitized: Clean the media -remove the data so it can’t be recovered by using normal system recovery utilities
In The Next Article, I will write About Security and Risk Management Written by : Mohamed Abdalla Ibrahim
PMP | CISM | ITIL | CEH | Azure Architect | Azure Security Engineer | IBM Cybersecurity Analyst