Chief Information Security Officer (CISO) responsibilities

Welcome to my blog! My name is Mohamed Abdalla Ibrahim and I am a Cyber Security Specialist and IS security enthusiast. With over 15 years of experience in an enterprise environment, I have a strong understanding of the business risks related to IT. I am always seeking out the newest technologies to upgrade my knowledge and enhance my skills and qualifications in my field. I am self-motivated and have strong communication skills, and my greatest goal is to be a distinguished source of innovation in the IT field. Thank you for visiting my blog, and I hope you find the information and resources on this site helpful and informative

let us assume that Today is my first working day as an information security officer and I would like to share with you my daily activity in my new job so you can learn really what we are doing and how we are doing I will show you how we are doing the following tasks in a real organization aka :
- Information security policy framework
- Information asset management
- Risk management
- Incident management
- Access control management
- Operation security
- vulnerability management network security
- Disaster recovery
- business continuity planning
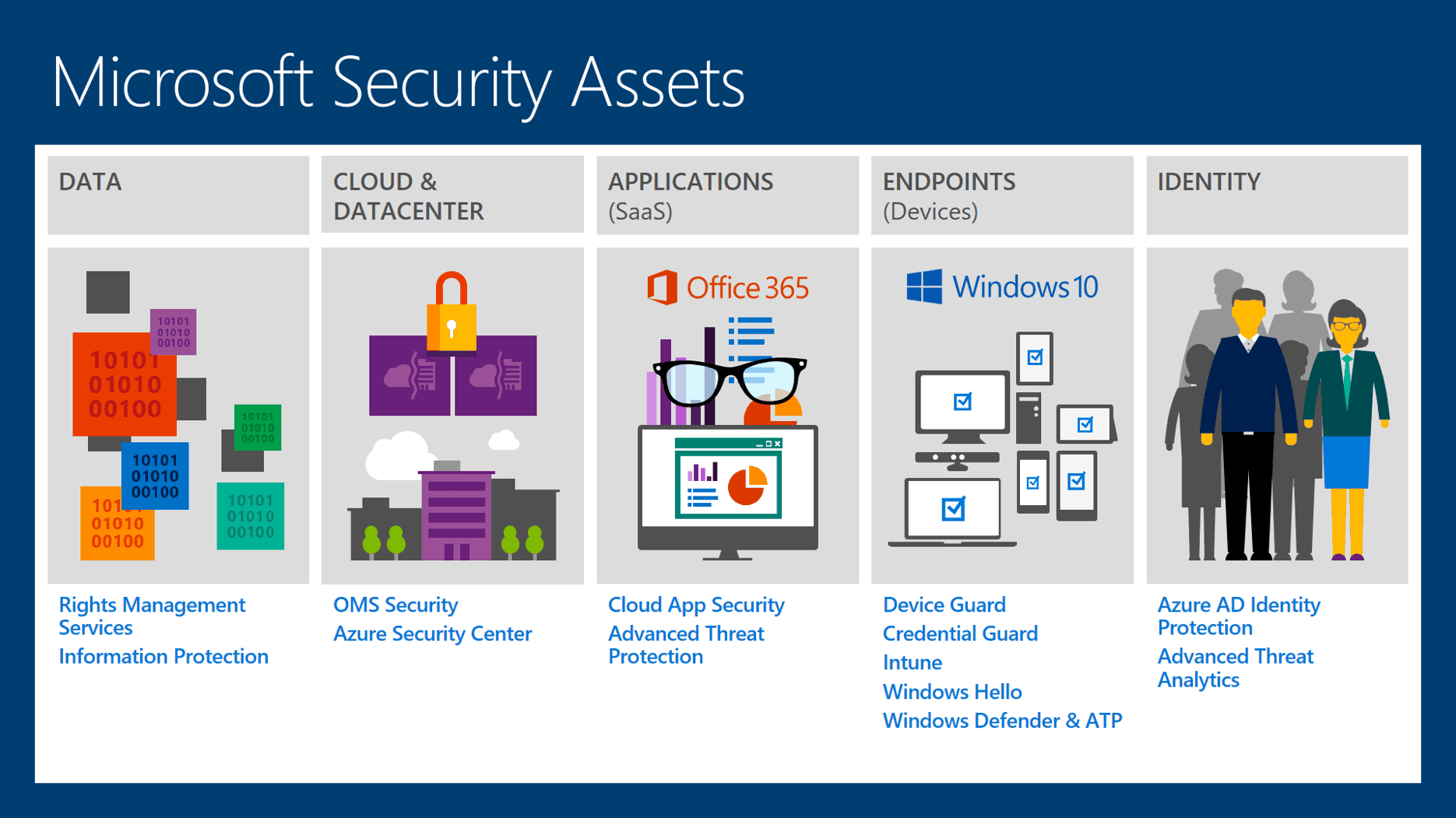
-> everything will be explained to you using real tools processes and documentation you will also learn how to manage solutions like :
- GRC
- Enterprise antivirus solution
- Enterprise DLP solution
- Data classification tool
- SIEM Solution

I’m also responsible to manage a few information security standards and compliance
- ISO 27001
- NIST
- PCI DSS
I will show you how we plan to implement and audit those standards and compliance and I will show you how we are doing some of those tasks in my company what tools we are using the challenges we are facing and what is the final deliverables by the end of each article I will raise a problem that we face at work.
So let's begin, before we started we had to know that the CISO's responsibilities are :
- Following standards compliance and regulation
- protecting the company information assets
- Managing risks
And :
- He should understand the company business very well what they are doing
- What service or product do they provide the company structure
- How many departments do they have
- Do they provide online services or only physical services
- Technical infrastructure to be able to implement security controls he had to have all those information

-> We don’t start from the technical implementation first we start to understand the business identify the critical business assets and functions and according to that we decide about the technical controls We don’t start from the technical implementation first we start to understand the business identify the critical business assets and functions and according to that we decide about the technical controls
-> let us assume that am working in a company and this company is an insurance company and they have five departments in a small workgroup network that include around 140 computers and laptops so brief they didn’t have security in place according to that I have to implement a full information security management system from scratch and the best way to do that is to implement ISO 27001 controls in my company ISO 27001 includes 140 controls some of them are technical and others are not we will learn the implementation of all the applicable controls from scratch if you need the resources you can email me and I will send it to you.
ISO 27001 classification controls are intended to:
-Deter: the control reduces the threat, deterring hackers from attacking a given system for example.
-Avoid: the control involves avoiding risky situations, perhaps ensuring that a known vulnerability is not exposed to the threat.
-Prevent: the control usually reduces the vulnerability (most common security controls act in this way).
-Detect: the control helps identify an event or incident as soon as possible, generally triggering reactive measures.
-React: the control helps minimize the impact of incidents by promptly and effectively reacting or responding to them.
-Recover: the control helps minimize the impact of incidents by aiding the restoration of normality, or at least a fallback service.
While the objectives of the controls are primarily to maintain the confidentiality, integrity, and/or availability of information.
Other classifications are possible. Furthermore, you may disagree with the particular way we have classified each control. However, we feel this is a pragmatic starting point for discussion. Feel free to modify this spreadsheet as you wish for your own purposes.
One way to use the spreadsheet is to identify and mark any controls that are excluded from your Statement of Applicability, in other words, those you have decided are not appropriate to your circumstances. Then look down the columns to check that you still have a sensible mix of different types of control. You may also use this spreadsheet when deciding how to treat identified risks, choosing a balanced set of controls giving defense-in-depth.
Written by : Mohamed Abdalla Ibrahim
PMP | CISM | ITIL | CEH | Azure Architect | Azure Security Engineer | IBM Cybersecurity Analyst