CYBER SECURITY (Penetration Testing Prerequisites) 1.1

Welcome to my blog! My name is Mohamed Abdalla Ibrahim and I am a Cyber Security Specialist and IS security enthusiast. With over 15 years of experience in an enterprise environment, I have a strong understanding of the business risks related to IT. I am always seeking out the newest technologies to upgrade my knowledge and enhance my skills and qualifications in my field. I am self-motivated and have strong communication skills, and my greatest goal is to be a distinguished source of innovation in the IT field. Thank you for visiting my blog, and I hope you find the information and resources on this site helpful and informative
 Welcome to my Penetration Testing Prerequisites course, in this article I will introduce you to information security, providing foundational skills on computer networks, protocols, web applications, and the penetration testing process. I transfer my experience to you as a junior pentester, you will be exposed to the technical aspects of systems, networks, and applications, where you will also gain a deep understanding of the differences between hacking, vulnerability assessment, and penetration testing.
Welcome to my Penetration Testing Prerequisites course, in this article I will introduce you to information security, providing foundational skills on computer networks, protocols, web applications, and the penetration testing process. I transfer my experience to you as a junior pentester, you will be exposed to the technical aspects of systems, networks, and applications, where you will also gain a deep understanding of the differences between hacking, vulnerability assessment, and penetration testing.
**The information Security Field : How Does this support my pentesting career :
- knowing the information security field
- career opportunists
- talking with colleagues
1.1 infoSec Culture : information security has a deep root in the underground hacking scene which looks at computer systems curiously, trying to figure out new ways to use and break them
Approaching systems curiously let hackers and infosec professionals find new ways to use computer systems, bypassing the restrictions imposed by software vendors or programs or deeply understanding any security pitfall of any kind of implementation
Note: being able to perform an attack also means being able to deeply understand the technology and function of the target system.

So being a hacker means being pushed by curiosity and having a hunger for knowledge, hackers explore, think out of the box, and improve their skills daily. "There is always something new to learn".
1.2 Career Opportunities:
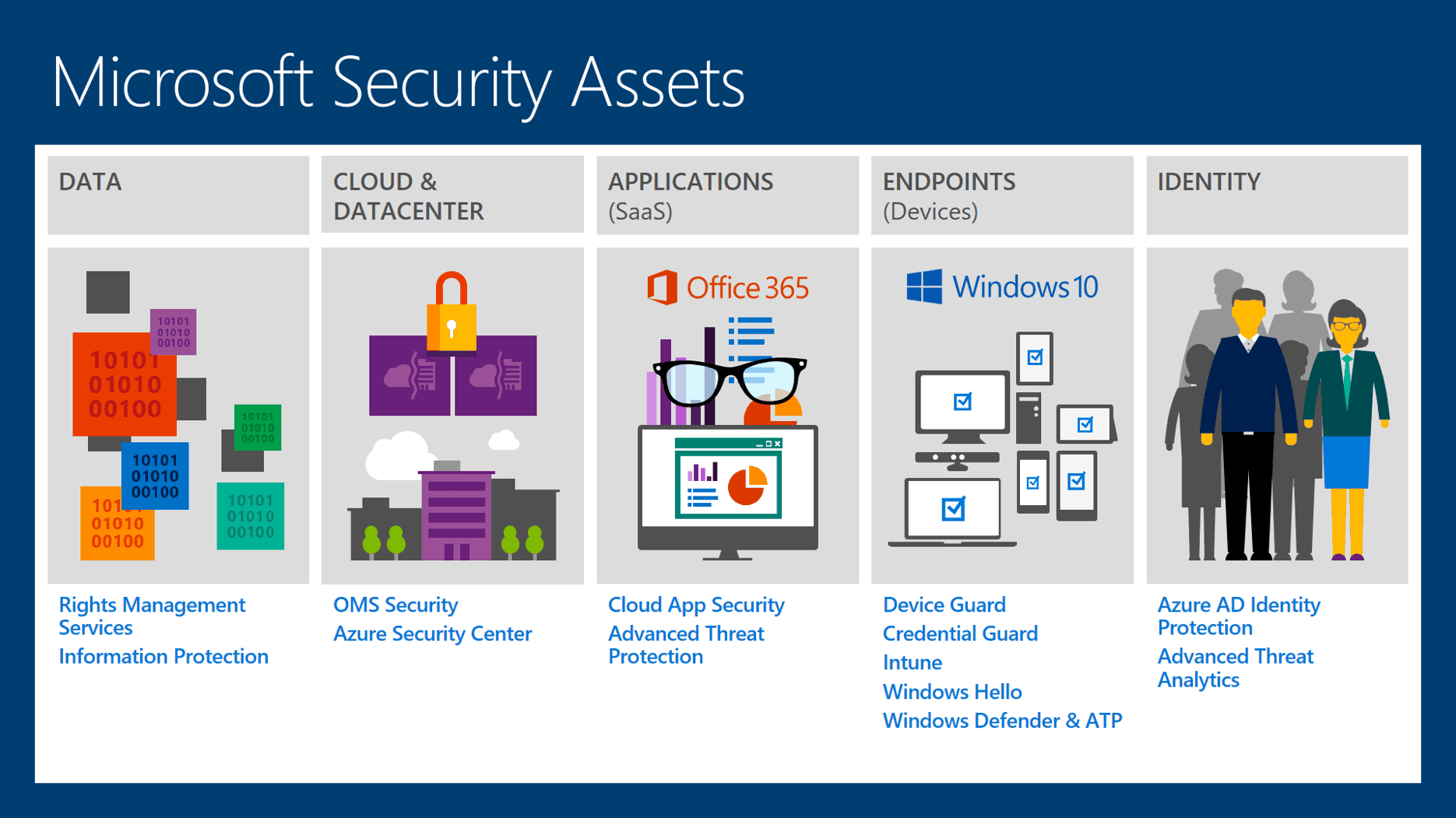
Nowadays, companies of all sizes, as well as government bodies, are using advanced technologies to store and process a great deal of confidential data on computers and mobile devices. Data is not only stored but also transmitted across private and public networks to other computers or mobile phones, therefore, its a must to protected sensitive information, I remember when I started my career 15 years ago security was a high need, day by day it's stated to increased and to become a must, companies invested thousands or millions to ensure their systems are protected, as I mentioned before most of the business are using Tech, so al least they should.
An Even more important sector is national security recently, the government has to face a range of cyber threats, global cyber syndicates, hackers for hire, hacktivist terrorists, and state-sponsored hackers. They are using their skills with the critical infrastructure like trains, dams, subways being controlled by computers, affecting the safety of nations.

Companies and Governments need to train their entire organization to make sure :
- Secure applications are developed
- proper defensive measures are tasked
- proper use of the company data in place
While IT security is a very difficult game! Away to ensure that a system is secure from cyber-attacks, from this point the PenTester role comes.
1.3PenTester : Are the professionals who are hired to simulate a hacking attack against a network, computer system, web application, or entire organization, using the same tools and techniques that malicious hackers use to discover any vulnerability in the system they are testing.
They can be specialized in specific infoSec such as : System attacks, ewe application, malware analysis, reserve engineering mobile application and so on.
Types Of Hacker:
- White Hat Hacker
- Black Hat Hacker

You must know the difference between two types :
 White Hat Hacker: is a professional penetrations tester or ethical hacker who perform authorized attacks against a system helping the clients to solve the security issues by closing vulnerabilities and avoid attacks, he is not performing illegal actions, you can say he is a good guy like Gandalf in Lord Of The Rings.
White Hat Hacker: is a professional penetrations tester or ethical hacker who perform authorized attacks against a system helping the clients to solve the security issues by closing vulnerabilities and avoid attacks, he is not performing illegal actions, you can say he is a good guy like Gandalf in Lord Of The Rings.
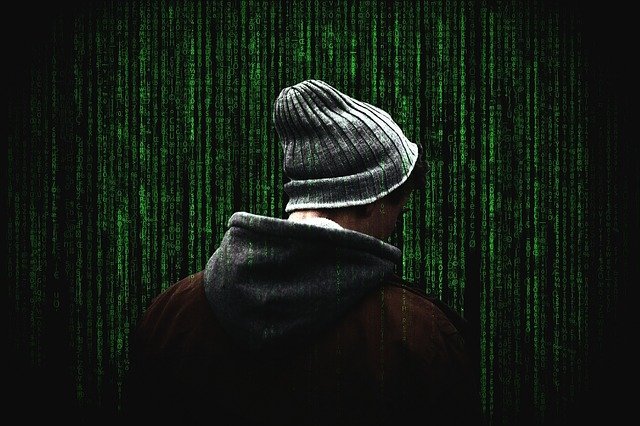
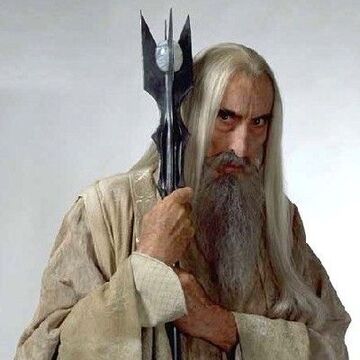 Black Hat Hacker: Is a hacker who performs unauthorized attacks against a system with the purpose of causing damage or gaining profit, you can say he is a bad guy like Saruman in Lord Of The Rings.
Black Hat Hacker: Is a hacker who performs unauthorized attacks against a system with the purpose of causing damage or gaining profit, you can say he is a bad guy like Saruman in Lord Of The Rings.
Note: both of them are using their magical skills one for good and one for evil.
You also must know, the difference between users and malicious users User: is a computer system user Malicious user: is a user who misuses or attacks computer systems and applications.
Root Or Administrator : are the users who managed an IT network or a single system, they have the maximum privileges over a system, the god of the system.
Some Examples of attacks :
- Getting unauthorized access
- stealing users password
- causing a denial of service
Anything that can harm a system is a kind of attack.
I will Dive deeper into attacks types in my next articles aka.
References :
Ine.com platform, Captain Crunch Wikipedia.com, The conscience of a hacker,
Written by : Mohamed Abdalla Ibrahim
PMP | CISM | ITIL | CEH | Azure Architect | Azure Security Engineer | IBM Cybersecurity Analyst